Delve sets the record straight on anonymous attacks
Maintaining customer trust is central to everything we do at Delve.
Over the past week, you may have seen a series of anonymous posts about Delve. Before we address the situation, we’d like to apologize for the inconveniences this has caused for our customers.
We moved quickly to scale and as we did, fell short of the standard we hold ourselves to.
For the last two weeks, our primary objective has been making sure customers feel confident in our platform and compliance outcomes. We’ve been working day and night to make improvements and have already implemented the following changes:
- Rebuilding our auditor network and removing firms that don’t meet our standards
- Offering complimentary re-audits and penetration tests to all active customers
- Halting any automation that interacts with audit workflows
- Enhancing transparency in audit communications by ensuring direct communication lines between customers and their auditors
- Making it unambiguously clear in the platform that templates (policies, board meetings, risk assessments) are designed to be starting points only
We’re grateful to the significant number of customers that are already working with us to complete re-audits and pentests.
Our team is on a mission to modernize compliance. As we grow, we are going to hold ourselves to the highest standard, not just in our product, but in how we communicate and operate. Over the next few weeks, we'll share platform demos to be even more transparent about how things work.
That said, there’s more to the story.
Evidence points to a malicious attack rather than a genuine whistleblower.
We've brought in leading cybersecurity firms to help us understand what happened.
Based on the available information, we believe that there was a coordinated, targeted cyberattack. It appears that an attacker purchased Delve under false pretenses, maliciously exfiltrated data, including Delve’s internal company data, and used it to launch a coordinated smear campaign against us.
.webp)
The above screenshot shows the attacker exfiltrating our audit tracking spreadsheet via file.io. This was later emailed anonymously to Delve customers and surfaced again in the Substack.
This is one of numerous instances of the attacker targeting our proprietary information. While we believe we were the primary target, we have notified customers we know were affected at this time.
We’re also actively working with leading cybersecurity firms to continue to strengthen our systems and protocols.
Beyond the criminal origin of the evidence, the posts are constructed to create fear and uncertainty around Delve.
The anonymous posts rely on a mix of fabricated claims, cherry-picked screenshots, and data taken out of context. For example, the post dismisses our AI while acknowledging it automated 70% of a security questionnaire, highlights a single manual integration while ignoring 600+ automated tests, and falsely claims we “stole” from another YC company when in reality we built on an Apache 2.0 open-source repository, which explicitly permits commercial use, and significantly rebuilt it for compliance use cases. They also mischaracterize our use of policy templates, which are standard across every compliance platform.
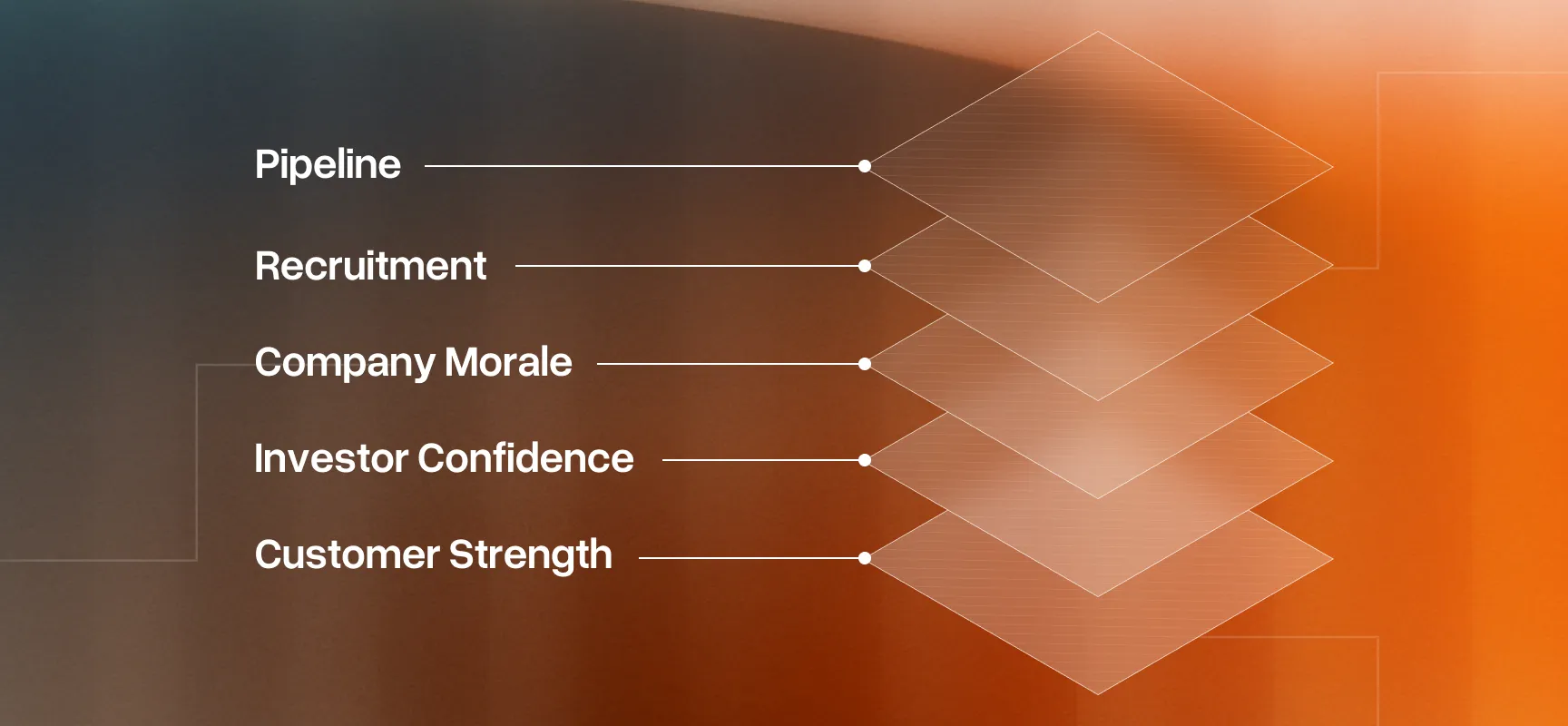
This framing is plainly designed to undermine confidence in Delve across customers, investors, team members, and auditors rather than reflect how the platform actually works.
Delve was built to modernize compliance. We are not going anywhere and are committed to building what's next.
- Karun and Selin
Maintaining customer trust is central to everything we do at Delve.
Over the past week, you may have seen a series of anonymous posts about Delve. Before we address the situation, we’d like to apologize for the inconveniences this has caused for our customers.
We moved quickly to scale and as we did, fell short of the standard we hold ourselves to.
For the last two weeks, our primary objective has been making sure customers feel confident in our platform and compliance outcomes. We’ve been working day and night to make improvements and have already implemented the following changes:
- Rebuilding our auditor network and removing firms that don’t meet our standards
- Offering complimentary re-audits and penetration tests to all active customers
- Halting any automation that interacts with audit workflows
- Enhancing transparency in audit communications by ensuring direct communication lines between customers and their auditors
- Making it unambiguously clear in the platform that templates (policies, board meetings, risk assessments) are designed to be starting points only
We’re grateful to the significant number of customers that are already working with us to complete re-audits and pentests.
Our team is on a mission to modernize compliance. As we grow, we are going to hold ourselves to the highest standard, not just in our product, but in how we communicate and operate. Over the next few weeks, we'll share platform demos to be even more transparent about how things work.
That said, there’s more to the story.
Evidence points to a malicious attack rather than a genuine whistleblower.
We've brought in leading cybersecurity firms to help us understand what happened.
Based on the available information, we believe that there was a coordinated, targeted cyberattack. It appears that an attacker purchased Delve under false pretenses, maliciously exfiltrated data, including Delve’s internal company data, and used it to launch a coordinated smear campaign against us.
.webp)
The above screenshot shows the attacker exfiltrating our audit tracking spreadsheet via file.io. This was later emailed anonymously to Delve customers and surfaced again in the Substack.
This is one of numerous instances of the attacker targeting our proprietary information. While we believe we were the primary target, we have notified customers we know were affected at this time.
We’re also actively working with leading cybersecurity firms to continue to strengthen our systems and protocols.
Beyond the criminal origin of the evidence, the posts are constructed to create fear and uncertainty around Delve.
The anonymous posts rely on a mix of fabricated claims, cherry-picked screenshots, and data taken out of context. For example, the post dismisses our AI while acknowledging it automated 70% of a security questionnaire, highlights a single manual integration while ignoring 600+ automated tests, and falsely claims we “stole” from another YC company when in reality we built on an Apache 2.0 open-source repository, which explicitly permits commercial use, and significantly rebuilt it for compliance use cases. They also mischaracterize our use of policy templates, which are standard across every compliance platform.
This framing is plainly designed to undermine confidence in Delve across customers, investors, team members, and auditors rather than reflect how the platform actually works.
Delve was built to modernize compliance. We are not going anywhere and are committed to building what's next.
- Karun and Selin
21-year-old MIT dropouts raise $32M at $300M valuation led by Insight

Related Posts
Don't let manual compliance slow you down.


.webp)



.avif)







.webp)