Complete CMMC Compliance Checklist

Key Takeaways
- CMMC compliance requires scoping your CUI environment, implementing security controls based on your level, documenting everything in an SSP and POA&M, and passing an assessment, with Phase 2 enforcement starting November 2026, making C3PAO certification mandatory for most DoD contracts.
- Scoping errors cause most assessment failures. Over-scoping wastes money on unnecessary controls, while under-scoping leads to automatic findings when auditors discover CUI in excluded systems.
- You need to pass at least 88 out of 110 controls for Level 2 certification. Any gaps go into a remediation plan that must be fixed within 6 months, or you lose certification.
- Training and policies fail more companies than firewalls. Assessors randomly interview your employees about CUI handling; any former employee who still holds active credentials is an automatic failure.
- Assessment costs $105,000-$118,000 for Level 2, not including the security tools and fixes you'll need to implement. Book your assessor 6+ months early because there aren't enough to go around.
- Certification lasts 3 years, but you must reaffirm compliance every year with False Claims Act liability for false attestation. One company paid over $8 million for lying about their compliance status.
- Organizations already compliant with NIST SP 800-171 can accelerate certification by 6-9 months since Level 2 maps directly to those same 110 controls.
When a DoD procurement officer asks for your CMMC certification status, and you don't have it, the deal stops. The Department of Defense published the final CMMC acquisition rule in September 2025, and Phase 1 enforcement began on November 10, 2025.
Cybersecurity Maturity Model Certification (CMMC) requires companies entrusted with Federal contract information (FCI) and controlled unclassified information (CUI) to implement cybersecurity standards at progressively advanced levels, depending on the type and sensitivity of the information. The program also describes the process required to protect information flowing to subcontractors. CMMC assessments enable the DoD to verify compliance with clear cybersecurity standards.
This guide provides the complete CMMC implementation checklist for 2026, from initial scoping through final certification, so you can secure contracts rather than watch compliant competitors win them.
Where CMMC Stands in 2026: Timelines and Requirements
Once CMMC rules take effect, certain DoD contractors handling FCI and CUI will be required to achieve a specific CMMC level as a condition of contract award. CMMC requirements will be implemented through a 4-phase plan over 3 years. By November 2026, third-party C3PAO certification will become mandatory for most contracts involving Controlled Unclassified Information.
CMMC rollout follows four phases.
- Phase 1 (November 2025): DoD includes Level 1 and Level 2 self-assessment requirements in solicitations.
- Phase 2 (November 2026): Level 2 C3PAO certification becomes mandatory for prioritized contracts.
- Phase 3 (November 2027): Level 3 requirements activate.
- Phase 4 (November 2028): Full implementation across all applicable contracts.
.webp)
Contracts already require CMMC via DFARS 252.204-7021 clauses. Program managers may, at their discretion, require C3PAO certification even during Phase 1 for high-priority programs. The gap between self-assessment and C3PAO certification (a third-party validation) determines your timeline. Self-assessment can be completed in weeks; C3PAO certification requires 6-18 months of preparation.
Step 1: Identify Your CMMC Level Based on Data Type
Check your contracts for DFARS clauses specifying CUI handling. If CUI is present, you need Level 2 minimum. Misidentifying your level wastes budget on unnecessary controls or worse, leaves you non-compliant at assessment.
Strategic consideration: Level identification isn't always straightforward. Contracts may reference CUI indirectly, or you may handle multiple contract types requiring different levels. A vCISO can review your contract portfolio, assess your data-handling practices, and recommend an appropriate level, preventing costly over-investment or compliance gaps that may surface during assessment. Or, you can start with Illumen's free CMMC scoping questionnaire.
Step 2: Scope Your CUI Environment and Define Your Boundary
Scoping defines your assessment boundary. This is where most failures originate.
Over-scope and you're paying for controls on systems that don't need them, which inflates costs. Under-scope and you'll fail when auditors discover CUI flowing through excluded systems. Map where CUI enters, moves through, and lands in your organization. Then categorize every asset.
Critical advisory point: Scoping decisions are irreversible once submitted to your C3PAO. An experienced vCISO brings assessment experience to help you navigate edge cases, including shared infrastructure, contractor-managed assets, and hybrid cloud environments. They can validate your boundary against the DoD Scoping Guide before you commit, potentially saving tens of thousands in unnecessary control implementation or preventing assessment failure.
The enclave approach segments CUI into an isolated environment, significantly narrowing your assessment boundary.
Critical cloud requirement: CSPs storing CUI must hold FedRAMP Moderate authorization and be listed on the FedRAMP Marketplace. Microsoft GCC High and AWS GovCloud hold this authorization. "FedRAMP equivalent" is a marketing term and does not satisfy DFARS 252.204-7012. Verify authorization directly on the FedRAMP marketplace.
Step 3: Implement the 14 Control Families (NIST 800-171 Breakdown)
Level 2 requires 110 controls across 14 families from NIST SP 800-171. Start with Access Control (22 controls covering MFA and least privilege) and Identification & Authentication (11 controls). These enable everything else. Then tackle Audit & Accountability, Configuration Management, System & Communications Protection, and System & Information Integrity for the technical foundation.
The remaining families cover organizational requirements: Awareness & Training, Incident Response, Maintenance, Media Protection, Personnel Security, Physical Protection, Risk Assessment, and Security Assessment.
Full control details: DoD CMMC Assessment Guide Level 2.
Step 4: Build Your Documentation Package (SSP, POA&M, Evidence)
You can't prove what you didn't document. Most assessment failures stem from documentation gaps, not technical deficiencies.
- System Security Plan (SSP) describes your system boundary, environment, and how each control is implemented. Must address all 320 assessment objectives. Generic templates won't work. Your SSP needs environment-specific details.
- Plan of Action & Milestones (POA&M) document lists unimplemented controls and your remediation timeline. Under CMMC, specific limited controls can be listed in the POA&Ms. Certain critical controls cannot be deferred. You need a minimum score of 88/110 to qualify for conditional certification. All POA&M items must be closed within 180 days, or certification lapses.
- Evidence artifacts include screenshots of configurations, policy documents, audit logs, training completion records, access review documentation, and vulnerability scan reports. It is better to organize by the control family for efficient assessor review. Stale evidence (older than the assessment period) may not be accepted.
- Network diagrams and data flows are the visual documentation of your CUI boundary, system interconnections, and data movement paths. This is required for scoping validation during the pre-assessment call. Inaccurate diagrams expand your assessment scope.
Step 5: Handle Organizational Controls (Policies, Training, Personnel)
This is where technical teams get blindsided.
- Policies aren't bureaucratic overhead. They're your contractual proof. You need approved policies for access control, acceptable use, incident response, change management, and media handling. These documents become legally binding commitments under your DoD contract. A vCISO can draft policies that are both compliant and operationally realistic, avoiding the trap of over-promising controls you can't sustain or under-specifying requirements that create liability.
- Training creates defensible evidence. Assessors will interview random employees. If your developers can't explain basic CUI handling procedures, that's a finding, regardless of how good your technical controls are. Every employee needs initial security training, annual refreshers, and role-specific training for anyone handling sensitive systems. Keep completion records; you'll need them.
- Personnel security closes the insider threat gap. Ensuring background screening before granting system access, obtaining a signed acknowledgment that employees understand their security responsibilities, and revoking immediate access upon departure. The last one trips up more companies than you'd expect. Former employees with active credentials are automatically found.
- Incident response gets tested. You need a documented plan with clear roles: who declares an incident, who investigates, and who reports to DoD within 72 hours per DFARS 7012. Assessors may run tabletop scenarios to verify your team knows the playbook.
- Change management protects your baseline. Every system modification needs approval before implementation, documented justification, and an audit trail. Undocumented changes to production systems raise immediate red flags during assessment.
Step 6: Deploy Your Technical Security Foundation
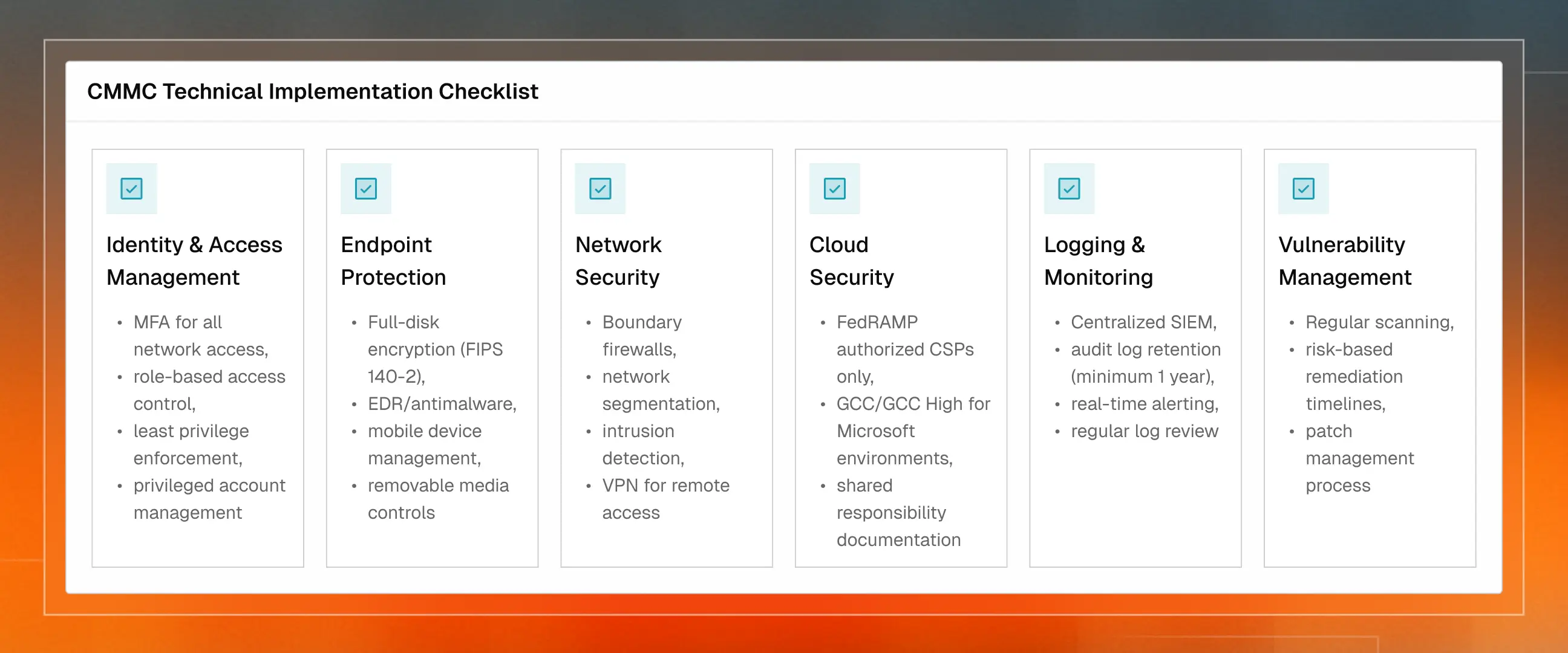
Following is a checklist of technical things your environment requires in Infrastructure, Cloud, and Security Tools for CMMC implementation.
Step 7: Navigate the Assessment Process (Self vs C3PAO)
Level 1 and non-prioritized Level 2: You evaluate each control as ‘MET’, ‘NOT MET’, or ‘NOT APPLICABLE’. Calculate your weighted score. Submit to SPRS. A senior official affirms compliance, which carries False Claims Act liability.
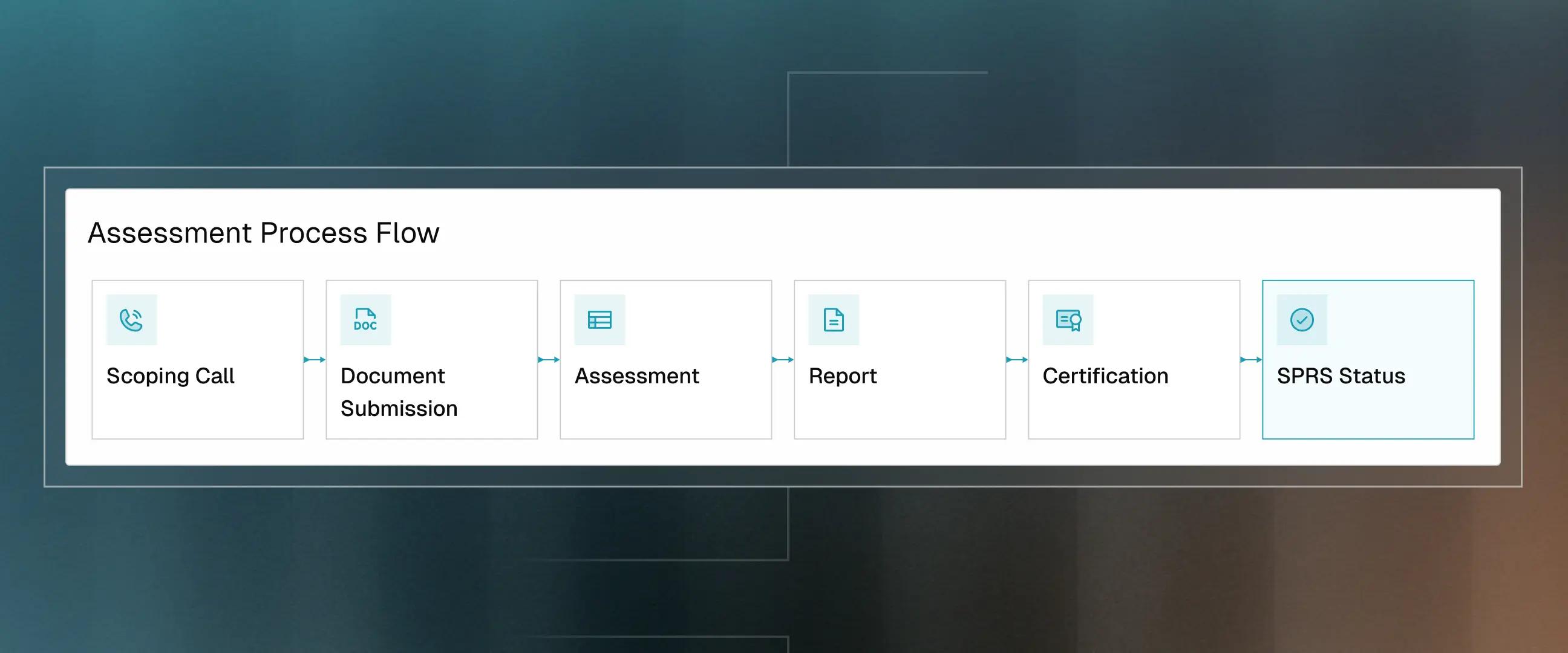
Prioritized Level 2 (C3PAO): A Cyber AB-accredited assessor C3PAO evaluates you. The process includes:
- Pre-assessment scoping call (approximately 30 days before assessment)
- Document submission (SSP, network diagrams, policies, evidence repository)
- On-site or remote assessment (interviews with key personnel, technical control testing, evidence sampling)
- Report uploaded to eMASS
You need at least 88/110 points for conditional certification. POA&M closeout required within 180 days or certification lapses.
Finding a C3PAO: Use the Cyber AB Marketplace. Verify they're authorized to assess. Book 6+ months in advance because capacity is tight.
Assessment readiness: Many organizations fail their first assessment due to preventable issues—poorly prepared personnel interviews, evidence gaps, or documentation inconsistencies. A vCISO can conduct mock assessments, prepare your team for assessor interviews, and validate your evidence package before submission. This pre-assessment review often identifies issues that would have resulted in findings, allowing remediation before the official assessment.
When to Engage vCISO Advisory vs. DIY Approach
Not every organization needs full-time advisory support, but strategic guidance at critical decision points can prevent costly mistakes. Start with Illumen's free CMMC scoping questionnaire to identify potential issues before committing to an assessment boundary. Consider engaging a vCISO when:
- You're making irreversible scoping decisions that will lock in your assessment boundary and control costs.
- You lack in-house CMMC assessment experience and need someone who's navigated the process before.
- Your contracts are ambiguous about CUI handling or required CMMC levels.
- You're developing policies that become legally binding commitments under your DoD contract.
- You're 3-6 months from assessment and need validation of pre-assessment readiness.
- You have complex environments (hybrid cloud, shared infrastructure, multiple subsidiaries) requiring nuanced scoping decisions.
- You need remediation prioritization to maximize your budget impact and ensure you hit the 88/110 threshold.
A vCISO can provide targeted guidance at specific milestones rather than full-time support, making advisory services cost-effective for organizations with existing security teams who need strategic direction rather than hands-on implementation.
Budgeting for CMMC: Realistic Cost Expectations
These figures are calculated by the DoD's cost analysis in the Federal Register.
These are assessment costs only. DoD explicitly excluded implementation costs because NIST 800-171 compliance has been required since 2017. The assumption is you've already invested.
Reality check: If you haven't been compliant, add remediation. Gap assessment typically runs $5,000–$20,000. Remediation and tools vary widely based on your gaps. Consulting support adds further costs depending on scope.
Cost-reduction strategies: The enclave approach can significantly reduce scope. Existing ISO 27001 or SOC 2 controls accelerate implementation. Starting early avoids rush rates.
Strategic advisory value: A vCISO can help prioritize remediation based on risk and assessment impact, ensuring you address critical controls first. They can also identify opportunities to leverage existing security investments and recommend cost-effective control implementations that satisfy multiple requirements. This risk-based approach often reduces total implementation costs by 20-30% compared to a sequential, control-by-control implementation.
Post-Certification: Maintaining Compliance and Continuous Monitoring
Certification isn't the finish line. It's the starting point for continuous compliance. CMMC is not a point-in-time audit you pass and forget.
- Annual affirmation: A senior official attests in SPRS that you maintain compliance. False attestation triggers False Claims Act liability. Recent settlements have exceeded $8 million.
- Continuous monitoring is ensured through automated control monitoring, regular vulnerability scanning, audit log review, and change management tracking. Manual processes create gaps.
- Documentation maintenance: Update SSP when your environment changes i.e. new systems, personnel changes, configuration modifications. Refresh evidence artifacts. Conduct periodic policy reviews. Stale documentation fails reassessment.
- Triennial recertification: Level 2 C3PAO certification is valid for 3 years. Plan your reassessment timeline 6 months before expiration.
- Supply chain monitoring: Your subcontractors handling CUI must maintain their own compliance. Their lapse can disqualify you.
12-Month CMMC Implementation Timeline
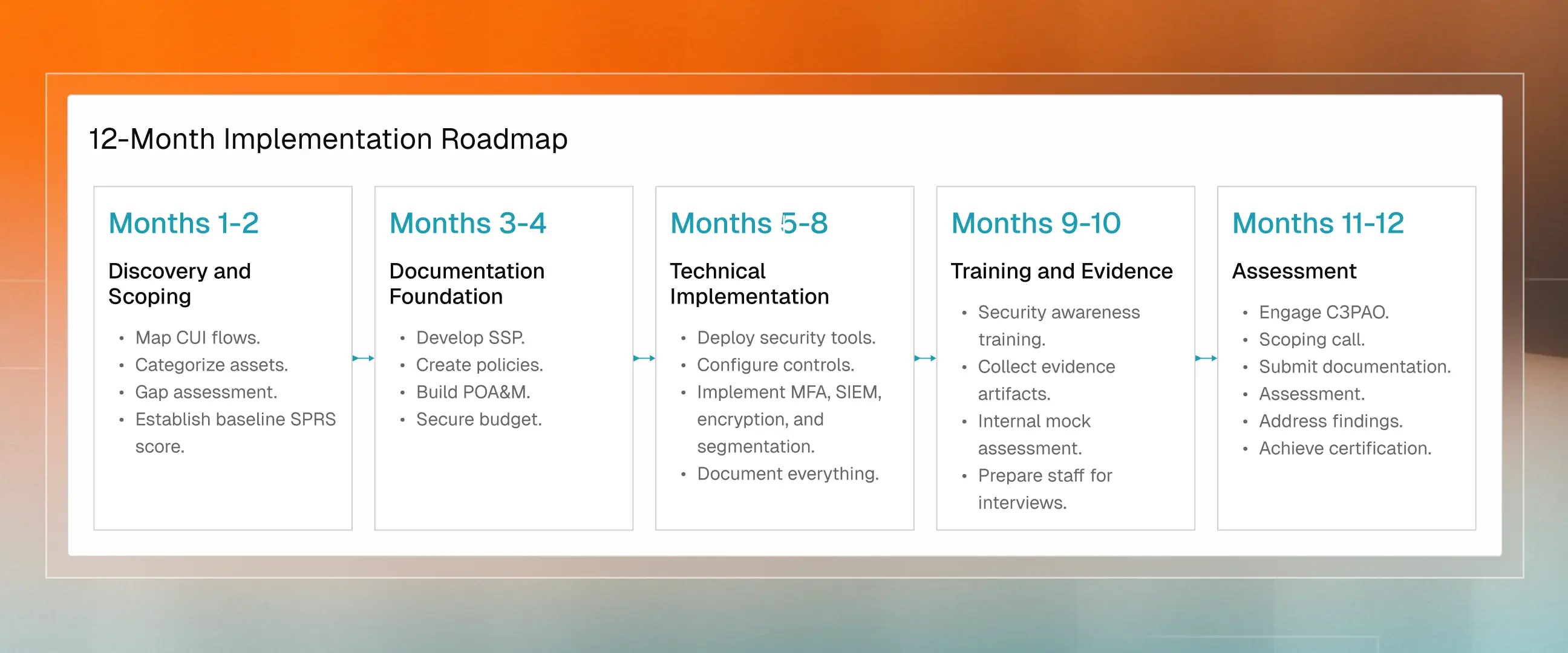
CMMC certification isn't just compliance; it's market access. Certified contractors pursue opportunities non-compliant competitors can't touch. Early certification means less competition while others scramble to meet deadlines.
The contractors winning work started early, scoped accurately, and built sustainable processes rather than one-time fixes. November 2026 isn't a target. It is a hard constraint approaching faster than most realize.
Delve helps defense contractors become CMMC-compliant and audit-ready fast. Our platform automates evidence collection, continuously monitors controls, and cuts documentation time in half. Our vCISO advisory network provides strategic guidance on scoping decisions, policy development, assessment readiness, and remediation prioritization, ensuring you avoid costly mistakes and pass your assessment the first time.
Schedule a call to see how the combined platform and advisory approach can compress your timeline from months to weeks.
Don't let manual compliance slow you down.